
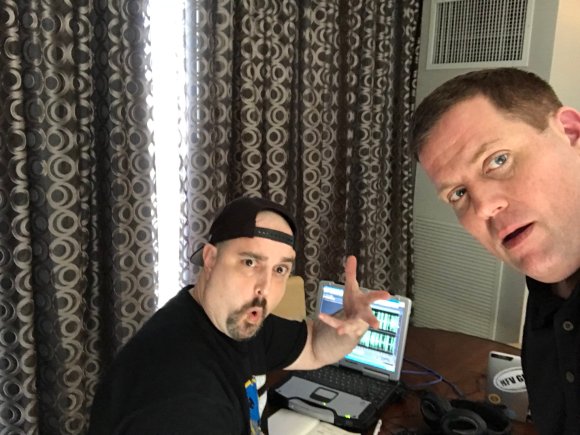
ICYMI: I moderated a BrightTALK webinar on the recent Google Docs phishing attack.
Join BrightTALK and check out this informative panel discussion featuring myself along with panelists Nathan Wenzler and Kowsik Guruswamy.
This slideshow requires JavaScript.
A massive phishing campaign targeting Google accounts ripped through the internet on a Wednesday afternoon in early May. Phishing scams are pretty common. What sets this scam apart is that it is more convincing than most. The email takes users who click on the file to a legitimate Google sign-in screen to grant permissions. If you received the email or are concerned you might be targeted next, join this interactive Q&A panel to get the facts and protect your account and your organization.
We discuss:
– What is the Google Docs email scam?
– How is this scam different from other phishing scams?
– What’s the deal with Eugene Pupov?
– Who’s at risk and how can you avoid being a victim?
– What can we expect in the future?
Moderator:
– Vince Tocce, Vince in the Bay Podcast
Speakers:
– Nathan Wenzler, Chief Security Strategist at AsTech Consulting
– Kowsik Guruswamy, CTO for Menlo Security
Follow me on Twitter!










 Guest –
Guest – 




 Guest
Guest 



