This episode is an interview with intelligence analyst Judy Towers and Michael Goedekr, CEO of hackdefnet, conducted over the summer at DEFCON 25 in Las Vegas (2017). Judy and Michael share their thoughts on threat intelligence, risk analysis, dealing with C suite executives and more.
Vince in the Bay
VITB 4 LYFE
Category Archives: cyber espionage
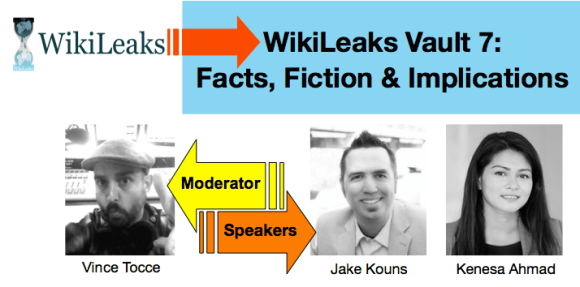
BrightTALK Webinar on WikiLeaks Vault 7
I recently moderated a BrightTALK webinar on the “Vault 7” CIA document leaks.
Join BrightTALK and check out this discussion titled “WikiLeaks Vault 7: Facts, Fiction & Implications” with distinguished speakers Jake Kouns (Risk Based Security) and Kenesa Ahmad (Aleada Consulting).
PODCAST: RSA Conference 2017

Another year, another wave of security incidents and threat models to keep the cybersecurity industry busy. So there was plenty to discuss and share as the InfoSec community flocked to San Francisco for the annual RSA Conference last month.

A view from the escalator as I descend into the bowels of RSAC 2017.
As always, the latest trends in the industry were addressed. Large data breaches, quickly growing threat models, security education, political hacking, and the risks posed by the Internet of Things were common threads throughout many of the keynotes, sessions, workshops, expos, and general chatter among attendees.
RSAC has more of a trade show feel compared to other security conferences so I’ve learned over the years that it’s best to approach the conference as an opportunity to meet and network with industry experts. This year I spent less time attending the talks and more time meeting with the players in the industry who are there to make deals and form partnerships.
However, I did catch several enlightening talks and panel discussions featuring the likes of ex-CIA operative Valerie Plame, security guru Bruce Schneier, researcher Rob Graham, people-security expert Masha Sedova, and security consultant Jeff Carr. Also enjoyed the entertaining keynotes by Late Night host Seth Meyers and astrophysicist Neil deGrasse Tyson.
CHECK OUT ROB GRAHAM’S TALK ON MIRAI AND IoT BOTNETS HERE!
Throughout the week I was lucky to catch up with several industry professionals representing some of the top tier firms in the cybersecurity sector who shared their take on the challenges and trends facing cybersecurity firms, their clients, and end users.
This episode of the podcast features interviews collected at RSAC 2017.
BIG THANKS TO THE GUESTS ON THIS EPISODE!!

Dave Lewis


Donald Meyer
Donald Meyer – Check Point Software

Dario Forte
- Sebastian Bortnik
- Alex Horan
- Selena Proctor
Sebastian, Alex and Selena – Onapsis

Scott Bollinger
Scott Bollinger – Security Researcher

Jeffrey Carr
DOWNLOAD FULL PODCAST MP3
SUBSCRIBE on iTunes, GooglePlay, Stitcher, and Soundcloud!!
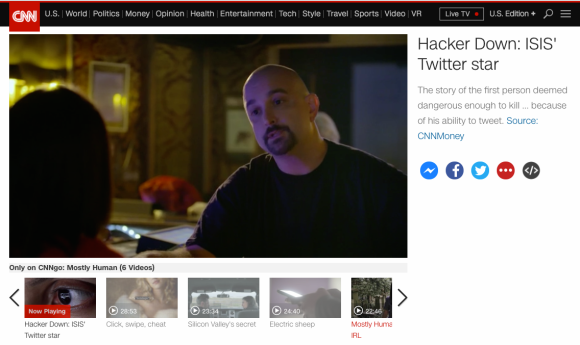
CNN’s “Mostly Human” Series Premier with VITB!
Look who’s in an episode of the new CNNgo series Mostly Human with Laurie Segall!
Here’s a link to the video:
http://www.cnn.com/videos/cnnmoney/2017/03/08/mostly-human-hacker-down.cnnmoney/video/playlists/atv-mostly-human/
PODCAST: Jon Nichols

Jon Nichols
Jon aka “@wvualphasoldier” is a security researcher, consultant, policy advisor and former US military PSYOP soldier. He served on and off the battlefield in Iraq and Afghanistan. We discuss the recent Shadow Brokers auctioning of computer network exploits which are alleged to have been stolen from NSA linked security firm, Equation Group.
TOPICS INCLUDE: Shadow Brokers, Equation Group, NSA, PSYOP, atmospherics, military intelligence, deception operations, propaganda, patriot hackers, The Jester, ISIS, Junaid Hussain (aka TriCk), Edward Snowden, Zipa Dux, insider threat vs. outside attacker theories, attribution, @thegrugq, Takashi Shimura, Rashomon and more!
DIRECT MP3 DOWNLOAD
SUBSCRIBE ON iTUNES
PODCAST: Jeffrey Carr
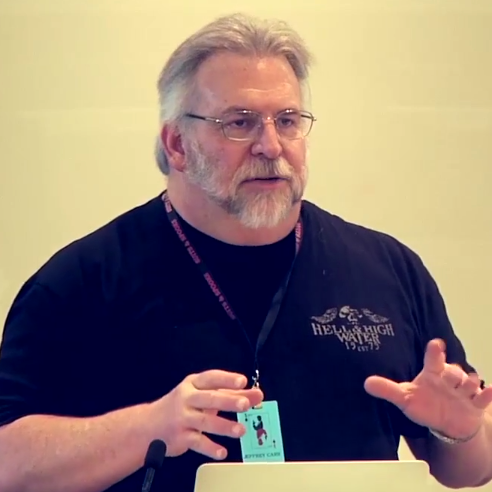
Jeff is a cyber security researcher, author of ‘Inside Cyber Warfare‘ (O’Reilly Media 2009, 2011), CEO of Taia Global, and Founder of the Suits and Spooks cyber security conference.
He joins Vince to discuss attribution in the wake of the DNC email leaks which are being attributed to cyber espionage by Russian intelligence agencies. Jeff recently wrote a medium post in response to attribution of the DNC hacks to the Russian government.
TOPICS INCLUDE:
Coastguard radioman :: stylistic analysis :: Shlomo Argamon :: Attribution :: Sony Pictures hack :: North Korea :: Russian hackers :: language analysis :: DNC leak/hack :: Thomas Rid :: Crowdstrike :: Fire Eye :: APTs :: cyber espionage :: Ukraine :: Swift on Security



 Guest
Guest